Many clients focus on a mobile app’s functions, features and aesthetics, but few emphasize the critical issue of mobile app security. Just one vulnerability exploitation can undo all the hard work and money you’ve invested to grow your user base. And once user trust is destroyed, it’s extremely difficult—if not impossible—to fully restore. Being proactive with your security will result in the life or death of your app.
This point was highlighted in the 2015 breach of the Starbucks mobile app, which was exploited to gain access to personally identifiable information (PII) such as credit and debit card info. The hacking prompted thousands to uninstall the app, converting one of the most frequently installed apps into one of the most avoided. Starbucks saw a similar security breach in 2017, again targeting their rewards program app. So mobile app security remains a real problem for even the largest corporations. In fact, the more prominent your brand name and the more users you have, the higher your risk factor.
Consumer-facing B2C apps are not the only apps that are susceptible. According to a 2016 study, 24.7 percent of B2B mobile apps include one or more high-risk security vulnerabilities, with business apps being three times more likely to leak login credentials. A 2016 study found that losses average $4 million dollars per incident or $158 for each piece of compromised data.
Gartner predicted that by 2017, 75 percent of mobile app security breaches would be rooted in-app misconfigurations—vulnerabilities that can be avoided by trusting your app to an experienced development team. There are several security features you should include in your mobile app, and contrary to popular belief, they’re not only necessary for high-risk applications. Strong security provides long-term savings by avoiding a costly hack or breach while promoting user confidence.
Single Sign-On (SSO) for Improved App Security
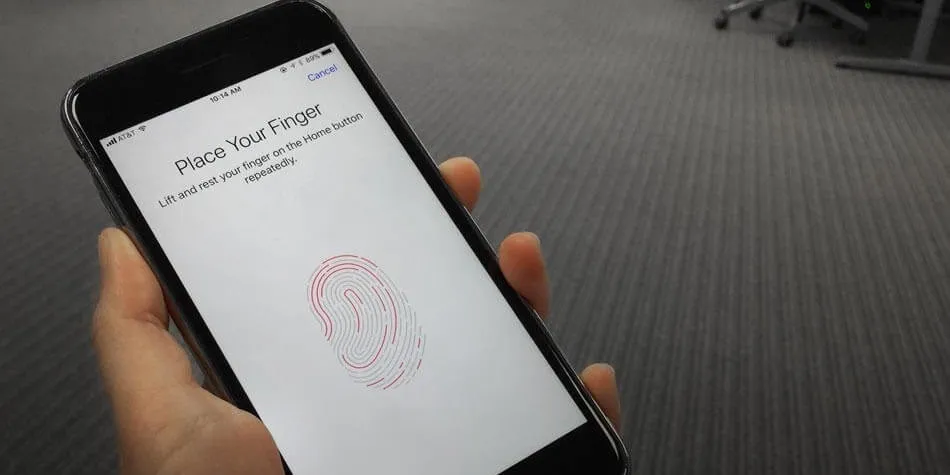
A single sign-on or SSO interface offers more than just increased security; it also improves user-friendliness. That’s because users log into the app using the same username and password they utilize on other platforms, such as Google, Facebook and apps/websites that use OpenID. Apple now provides a new spin on SSO with its TouchID authentication technology, which lets you use your fingerprint in place of a username and password.
Traditionally, single sign-on leverages XML-based authentication technology called Security Assertion Markup Language (SAML). And while SAML was suitable for desktop apps, the greater complexity of mobile applications demanded a new approach. Enter cloud-based authentication services, including Google Apps, Microsoft Azure and Amazon Web Services, along with Enterprise Mobility Management (EMM) and Mobile Device Management (MDM) services.
With modern SSO technology, apps prompt you to enter your login credentials through a third-party sign-on and authentication interface upon launch. The third-party interface then issues a certificate to the smartphone or another device to “unlock” one or multiple apps on the device. SSO is like having a single key that works on several doors.
This allows mobile app developers to leverage a third party’s more sophisticated authentication technology. You also enjoy greater user confidence since most consumers are familiar with single sign-on services like Google and TouchID. Virtually any app can benefit from this technology.
Boosting App Security With Biometric Authentication
Biometric authentication is an emerging form of technology that is gaining popularity thanks to the challenges associated with bypassing biometrics. Apple’s iPhone was the first mainstream consumer device to feature biometric authentication. The TouchID-equipped iPhone 5S was unveiled in the Fall of 2013.
Basically, biometric authentication is any form of authentication that uses a scan of a unique part of the body to verify identity. While most are familiar with fingerprint-based biometric authentication, technology is in development for more foolproof forms, including:
- Iris scans;
- Voice recognition;
- Facial mapping; and
- Signature recognition.
Biometric authentication is amongst the most reliable mobile app security measures because it’s challenging to steal a person’s iris or fingerprint. The most sophisticated fingerprint scanners, which can be connected to a mobile device for biometric authentication, look at more than just fingerprint whorls and patterns. They also detect temperature and skin conductivity. This technology will likely be integrated into future incarnations of the iPhone, along with other devices.
The majority of apps can benefit from biometric authentication, although we primarily see this technology in apps that demand high-level security, such as banking apps, trading apps, and smart home apps. It’s predicted that apps will eventually take the place of keys and fobs, so we’ll likely see biometric authentication in these applications in the future.
Notably, fingerprint scanning technology is not universally available on all Android mobile devices, making it impractical to use biometric authentication as the only sign-in option in hybrid apps or native Android apps.
Improved Security With Two-Step Authentication
Two-step authentication—also called multi-factor or two-factor authentication (2FA)—is becoming more common in a range of apps, from social media apps to enterprise apps to e-commerce apps. It simply requires the user to perform two tasks to complete the login process. Some common examples of two-step authentication include:
- Enter a username and password + Enter a code or security token sent to your mobile phone;
- Enter a username and password + Enter a code or security token sent to your email;
- Enter a username and password + Answer a security question;
- Enter a username and password + Verify the login on another connected and verified device; or
- Enter a username and password + Verify your identity with biometric authentication.
Two-factor authentication is regarded as more secure than single-factor authentication because, given sufficient time and resources, most username/password combinations can be uncovered using a sophisticated hacking script.
Since hackers must pass through two checkpoints instead of one, users can feel greater confidence in the mobile app. This peace of mind is vital for apps that store personal information, financial data or afford financial access (i.e. a mobile banking application.) Many developers also include two-factor authentication as an optional feature when family and friends (not hackers or data thieves) represent the most significant security threat, as in the case of a social media app.
SSL Encryption for Mobile Apps
Secure sockets layer (SSL) encryption is often viewed as optional, but we have advanced to a degree where every mobile app should feature this form of encryption. SSL technology encrypts the data that travels between the mobile app and the server. Data is vulnerable when in transit, but encryption renders traveling data useless to anyone who intercepts it.
Many mobile developers, including the 7T team, opt for 4096-bit SSL encryption, which offers military-grade security to provide the highest level of confidence.
Remote Wipe Capabilities for Your Mobile App
Remote wipe capabilities are essential for any app storing data that could be valuable to a hacker. A remote wipe allows you to delete an app and all associated data, even if you don’t have access to the physical device.
Most mobile apps store a significant amount of data on the actual device, which speeds load time and improves responsiveness. But, within convenience lies a major vulnerability: many apps remain open indefinitely after launch, so anyone who unlocks your device can potentially access your in-app information. This makes a remote wipe feature especially important if you have not integrated an automatic time-out after a few minutes of inactivity. Remember, it’s relatively easy to access sensitive data once you have the actual device in-hand. You don’t even need high-level tech knowledge; it can be as simple as resetting a password via email, as many leave their email app open.
Although a remote wipe feature can prevent unauthorized access to sensitive information, this feature is less critical for apps that employ the following security measures:
- The app automatically logs out users after a short period of inactivity.
- There is no email password reset feature; and
- The app keeps all data on the device in encrypted form.
A remote app wipe allows users to avoid a full wipe, which may be their only other option if the mobile device is taken or misplaced. This feature is also useful for ensuring data privacy requirements, such as those set forth under HIPAA.
Mobile App Security for Financial Transactions
Transaction security refers to measures to protect transactions, such as a purchase, sale or stock trade, from fraud, cyber attacks and vulnerability exploitations. It’s wise to use many of the aforementioned technologies in tandem to ensure your mobile app is secure. Transaction security measures include:
- Using two-factor authentication and/or biometric authentication to verify user identity prior to initiating the transaction;
- Encrypting data during the most vulnerable phases of the transaction;
- Encrypting all stored data on the user’s device and at the server level, particularly financial info and funding sources;
- Using advanced SSL technology when communicating with a server;
- Requiring biometric authentication to complete the transaction;
- Automatic logout after a period of inactivity; and
- Remote data wipe capabilities.
Mobile App Security Vulnerabilities and the Internet of Things (IoT)
Mobile apps that interact with other devices via the IoT require additional security and more comprehensive testing to identify and patch vulnerabilities. One significant issue was discovered in early 2017 when Hyundai’s Blue Link app had a major vulnerability. If exploited, it would allow cyber attackers to start the vehicle from anywhere with an internet connection. The vulnerability centered around insecure WiFi connections, which could be used to obtain a driver’s username, password, and PIN number—the info required to locate, unlock and start the car.
Fortunately, Hyundai’s Blue Link app vulnerability was identified before cybercriminals could exploit it. But Hyundai hasn’t been the only carmaker to discover a major security flaw. In 2015, Fiat Chrysler issued a recall affecting over 1.4 million vehicles after a major “hole” was found in the UConnect Infotainment system that would allow cyber attackers to remotely control the vehicle’s braking and steering.
These incidents underscore the importance of utilizing all available security measures and performing in-depth vulnerability testing to enhance mobile app security, particularly those with IoT integration since a compromised app could serve as a gateway to multiple systems. Ensuring security requires a mobile app developer experienced with cutting-edge technology; a developer like 7T, who is committed to providing clients with state-of-the-art apps featuring all the security you and your users need. In fact, every app we build is equipped with multiple levels of military-grade mobile app security. Contact us today to discuss your company’s mobile security needs.